AI penetration testing: Why API-first architectures demand a new testing model

The traditional penetration testing model is breaking. For a long time, the gold standard was the annual or biannual manual penetration test assisted by automated tools.
A security consultant would spend two weeks probing your perimeter, hand you a 60-page PDF, and leave. You prepare fixes for the next release, or if a problem is deemed critical enough, a “hot fix” is applied.
As organizations move toward API-first architectures and CI/CD pipelines, the gap between deployment speed and security oversight is becoming a chasm. AAI penetration testing closes this chasm. It leverages machine learning and autonomous agents to continuously validate security at the pace of software development.
However, not all AI pentesting solutions are designed for API-driven environments. While organizations focus on the surface web, that is, UI-based applications, the true risk lives in the underlying infrastructure: the APIs. So, to secure a modern stack, you must do two things:
- Go beyond the UI and focus on your APIs.
- Recognize that testing APIs requires an approach with a contextual understanding of the complexity of the API.
But before exploring why APIs require a different testing model, we must first understand what AI penetration testing entails.
What is AI penetration testing?
AI penetration testing is the use of artificial intelligence to automatically discover, test, and safely validate the exploitability of security vulnerabilities.
Traditional vulnerability scanners, such as ZAP, rely primarily on predefined rules, signatures, and fuzzing techniques.
Conversely, AI penetration testing actively explores an application in ways that mirror the behavior of a skilled human penetration tester, but at a far larger scale repeatability. It autonomously analyzes endpoints, learns how an application behaves, explores access control patterns, launches attacks, and produces replicable findings.
Key characteristics of AI penetration testing
AI pentesting must include, at the very least, the following:
- Autonomous probing: An AI pentesting solution operates with minimal human involvement, autonomously mapping applications and launching attacks calibrated to the particular target.
- Attack path discovery: It understands that a vulnerability in
Endpoint Amight be the key to escalating privileges inEndpoint B, regardless of how innocuous it appears. Accordingly, instead of testing isolated endpoints, an AI pentesting solution seeks to identify possible multi-step attack paths across an application. - Intelligent payload generation: AI creates test cases based on observed application behavior. For example, rather than throwing random strings at an input, the AI learns the expected data format and crafts malicious requests that look legitimate to the server.
- Continuous security testing: AI penetration testing runs continuously, allowing you to discover vulnerabilities introduced by new releases and configuration changes.
How AI penetration testing works
The workflow of AI penetration testing mirrors the methodology of elite application security professionals but compressed from weeks to hours or minutes.
Asset discovery
The process begins with the discovery of accessible assets. In the API context, the AI ingests your OpenAPI/Swagger specs, sniffs traffic, or interacts with endpoints to find:
- Public, private, partner, or composite APIs
- REST, GraphQL, SOAP, gRPC, or WebSocket API endpoints
- Multiple API versions, including still accessible zombie APIs
- Hidden or undocumented, that is, shadow APIs
Visibility is a critical factor in any cybersecurity endeavor, and AI penetration testing is no exception. Comprehensive asset discovery is the prerequisite for a successful AI penetration test.
Endpoint relationship mapping
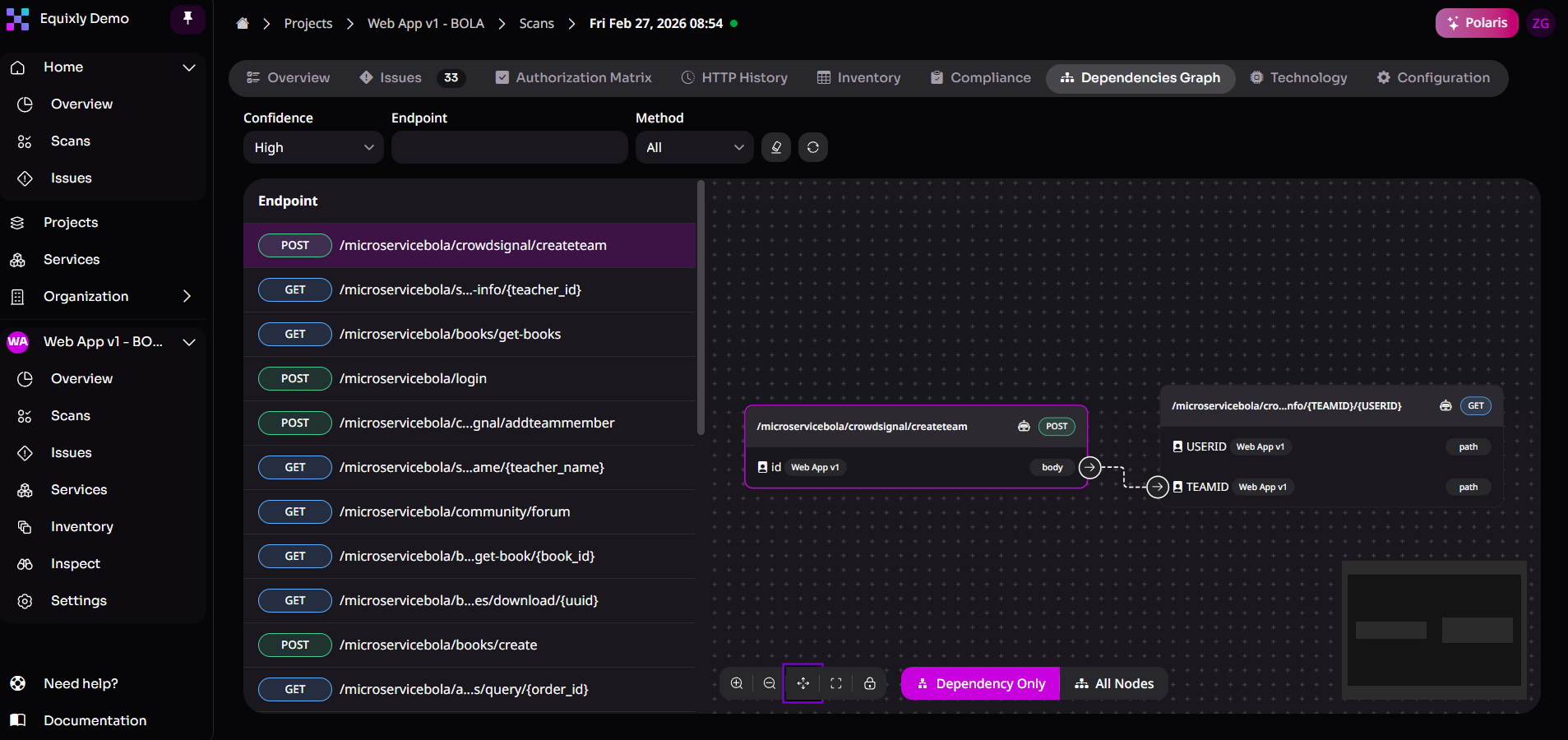
After discovery, AI systems build a model of the application structure, figuring out:
- Endpoint names and descriptions
- Data flows
- Parameter types
- Request patterns
- Response structures
At this stage, the AI pentesting tool makes observations such as “GET /user/profile is linked to POST /account/settings”, allowing it to understand how your APIs are intended to behave.
Authentication learning
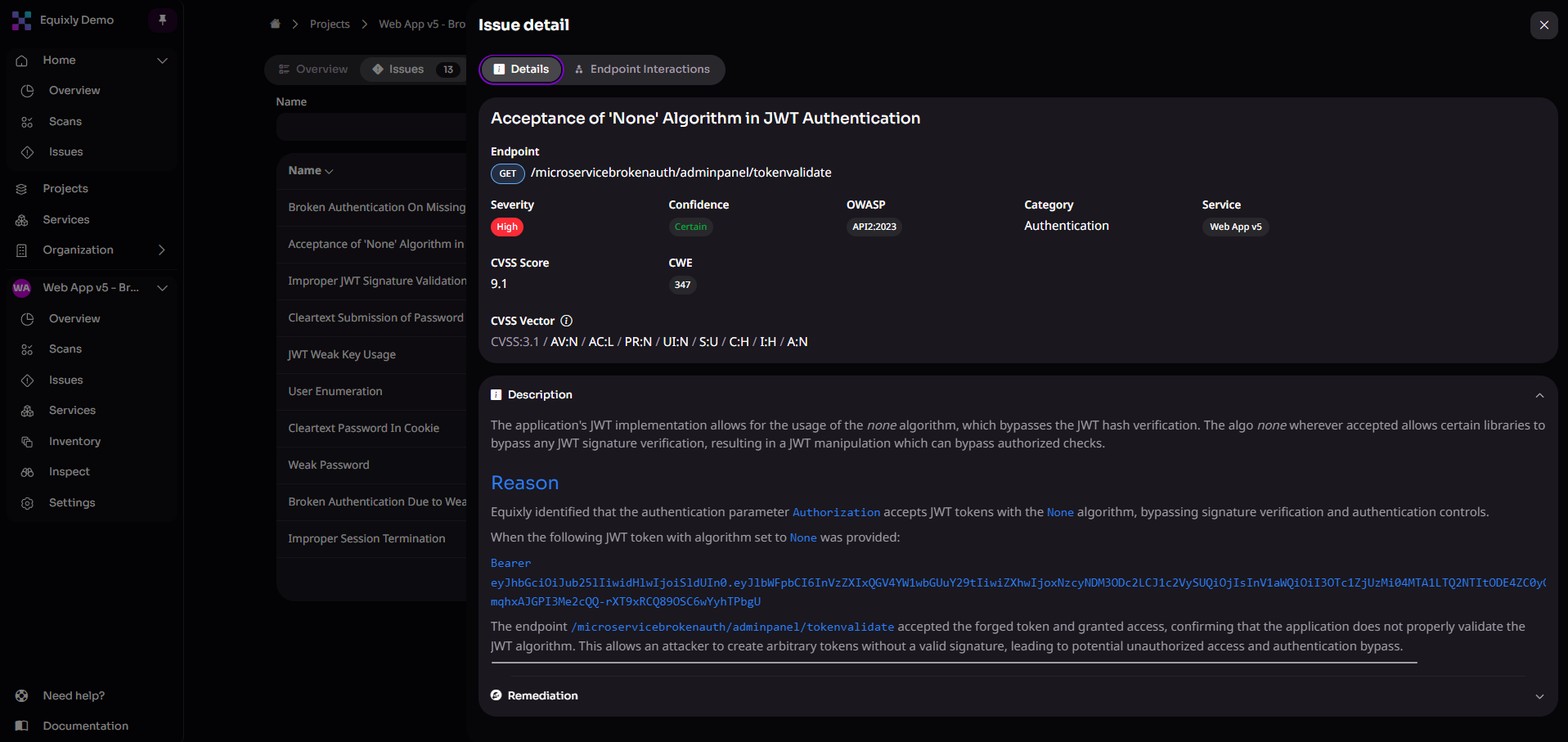
AI analyzes how authentication works by examining mechanisms such as:
- JWT
- API keys
- OAuth workflows
- Login sequences
- Authenticated sessions
It attempts to bypass or manipulate authentication tokens, testing for security vulnerabilities at multiple privilege levels, from a regular user to an admin.
Attack emulation/simulation
Once they build the application model, AI systems attempt attack scenarios, such as:
- Business logic abuse
- Remote code execution
- Data exfiltration
- Privilege escalation
- Account takeover
It’s absolutely worth noting that AI penetration testing adapts based on results. This is key, as it allows it to find new attack paths, as well as expand and explore successful attack patterns further.
Exploit validation
AI penetration testing validates vulnerabilities to demonstrate whether exploitation is a realistic and impactful possibility. An effective AI pentesting tool can go over myriad different scenarios, including:
- Business logic vulnerabilities (BOLA, BFLA)
- Authorization bypass
- Parameter tampering
- SQL injection
- Insecure direct object reference
- Server-side request forgery
This step decreases the risk of wasting time on inconsequential threats, which reduces noise for both security and development teams.
Traditional penetration testing vs AI penetration testing
Traditional penetration testing has been the industry standard for decades, and rightly so. Claiming it has lost its value today is preposterous. But denying that it has grave limitations in modern digital environments is as preposterous.
Strictly from a cybersecurity perspective — putting aside for the moment factors like cost and duration — the biggest downside of a traditional penetration test is that it’s a snapshot in time. As such, the relevance of its results is inversely proportional to the time elapsed since the last test.
Modern development teams deploy updates weekly, sometimes daily. And due to deadlines and pressure, the very next software release could accrue a whole stack of vulnerabilities. Accordingly, a penetration test you conducted 12, 6, or 3 months ago does not reflect your current attack surface and security posture.
AI penetration testing, on the other hand, enables precisely that: keeping pace with development and gaining ongoing insights into your actual security posture. That’s because AI can work consistently around the clock without interruption. Moreover, in time, many systems can improve testing strategies through model updates and accumulated training data.
And when you factor in other variables, the comparison between traditional and AI penetration testing looks like this:
| AI Pentesting vs Traditional Pentesting Comparison | ||
|---|---|---|
| Factor | AI Pentesting | Traditional Pentesting |
| Frequency | Continuous | Annual, biannual, or quarterly |
| Cost | Low and predictable | High and unpredictable |
| Coverage | Extensive | Limited |
| Speed | Hours | Weeks |
| Human effort | Minimal | Heavy |
| Depth | Exhaustive | Selective |
While AI penetration testing improves security validation in general, its value becomes particularly clear in API-driven environments.
Why AI pentesting must adapt to API-driven architectures
What makes AI pentesting invaluable and necessary for enterprises, whose software typically hinges on a plethora of APIs?
APIs have a convoluted attack surface
An API-driven application in an enterprise environment can contain:
- Hundreds of endpoints
- Multiple API versions
- Third-party integrations
- Many internal microservices
Numerous endpoints may not be visible through a browser interface, documented, or retired. This state creates not only a large but also a convoluted attack surface plagued by high obscurity.
In such conditions, AI penetration testing at scale — that is, pentesting assisted by artificial intelligence and machine learning — is one of the most effective ways to continuously explore large API attack surfaces.
APIs depend on complex auth
Organizations typically secure APIs using mechanisms such as:
- OAuth 2.0
- JWTs as access or identity tokens
- API keys
- Session tokens
- Cryptographically signed requests, such as HMAC-based request signing
Each of these mechanisms can suffer from different vulnerabilities. The differences may be subtle, but they are highly important and relevant in a testing context.
On top of this, probing authorization requires:
- Multiple user roles
- Token manipulation
- Session analysis
- Privilege testing
Again, purpose-built AI penetration testing is one of the most scalable approaches to achieving deep authentication and authorization testing coverage across multiple roles and token types.
APIs change constantly
As said before, API-first organizations deploy frequently, adding endpoints and changing parameters. As they deploy new services and modify existing ones, every aspect of the underlying APIs changes.
To re-emphasize a point we’ve made earlier, how can pentesting performed annually or even quarterly keep up with these dynamics? Continuous pentesting is, indeed, the feasible and viable way to test APIs after every release.
APIs demand state-aware testing
API vulnerabilities often appear only within the context of multi-step interactions. A single request can look perfectly benign, but its position within a sequence of calls may reveal deep architectural flaws — most notably broken object level authorization (BOLA).
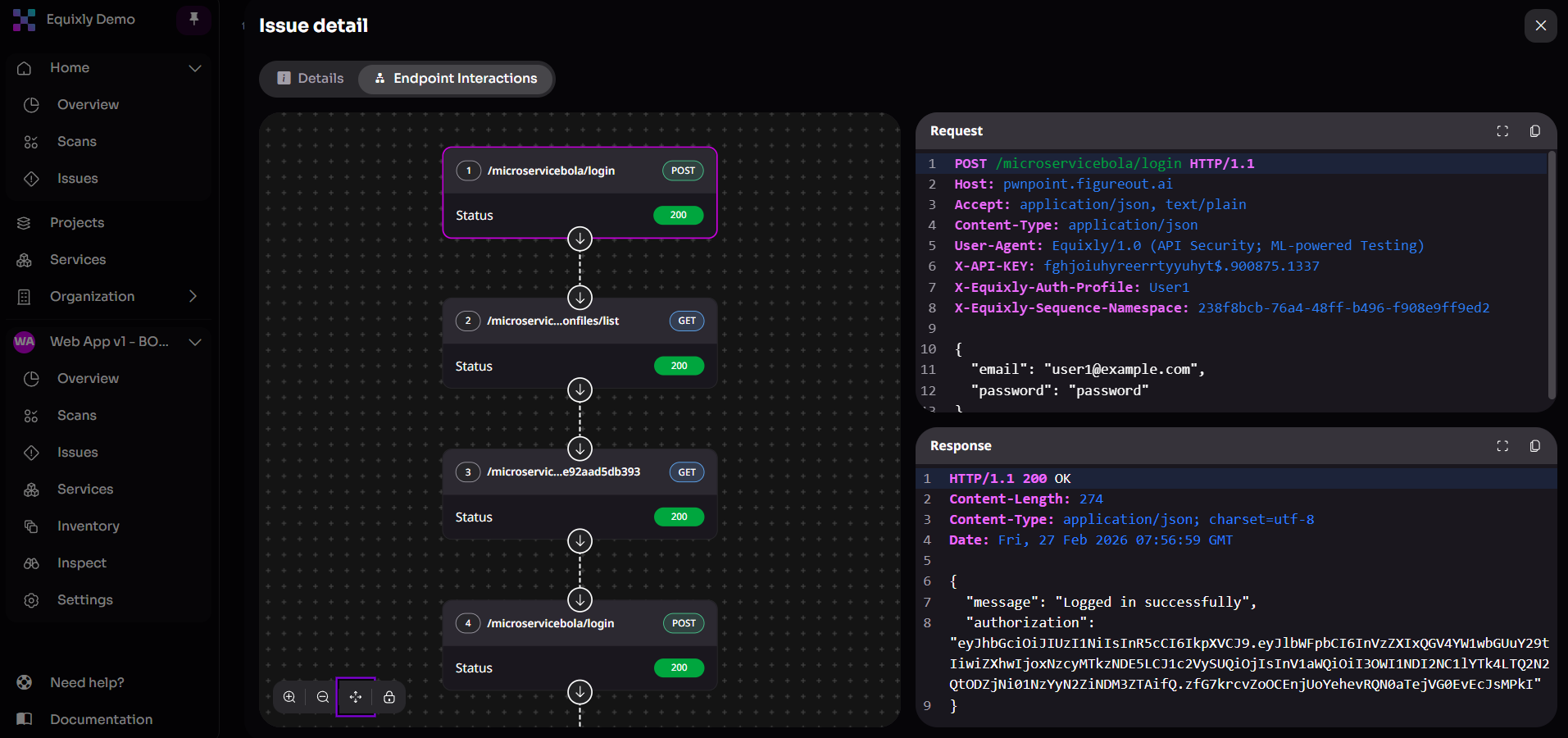
An offensive approach tailored for APIs includes techniques such as:
- Request sequence testing: Execute logical chains of events —
Create → View → Edit → Delete— to identify where authorization checks are missing in a resource life cycle. - Authenticated session persistence: Maintain and manipulate user contexts (
Adminvs.User Avs.User B) throughout those sequences to verify that data isolation remains intact. - Dynamic state tracking: Capture values from responses, such as a
resource_idortransaction_token, and reuse them in subsequent requests to mimic the behavior of both legitimate and malicious users.
This ability allows AI to emulate the persistence of a real-world attacker, uncovering vulnerabilities that only trigger when the API is put through complex logic flows.
Limitations of AI penetration testing
AI penetration testing dramatically improves the speed, scale, and consistency of security validation. However, like any security technology, it has practical limitations and works best as part of a broader security strategy.
Not a full replacement for human expertise
In practice, an AI pentesting platform can autonomously perform the vast majority of API security testing tasks, but it works best when combined with human knowledge and experience.
Security specialists are invaluable in scenarios that demand deep, bespoke research or highly narrow expertise, such as:
- Complex architectural security reviews
- Advanced threat modeling for novel systems
- Red team engagements simulating sophisticated adversaries
- Corner-case logic flaws that require extended manual investigation
As a result, the strongest security programs combine continuous AI-driven testing with targeted expert analysis for the most complex scenarios.
Requires proper setup
AI pentesting delivers the best results when systems are properly configured for testing. For example, effective testing environments typically include:
- Correctly configured authentication mechanisms
- Accessible APIs and endpoints
- Test environments that safely replicate production systems
Without adequate setup, the AI system may have limited visibility into the application, thereby missing elusive or obscure vulnerabilities.
Works best with context
AI testing becomes significantly more effective when it has access to contextual information about the tested API applications. Useful inputs include:
- API specifications (such as OpenAPI or Swagger)
- Test accounts for authentication workflows
- Multiple user roles to evaluate authorization behavior
Providing this context allows the AI system to explore deeper attack paths, test role-based access controls, and simulate more realistic attacker behavior.
When you need AI penetration testing
AI penetration testing is especially well-suited for organizations operating complex digital systems with dynamic and difficult-to-assess attack surfaces. Examples of the main types falling within this category are:
- API-first SaaS companies
- Firms running large microservices-based architectures
- Fintech firms
- Healthtech providers
- Utilities operating critical infrastructure and connected operational technology (OT) systems
- E-commerce platforms and digital marketplaces
- Companies exposing public developer APIs or partner ecosystems
You should strongly consider embracing AI pentesting if your organization experiences any of the following:
- Frequent production releases or continuous deployment pipelines
- Extensive or quickly growing API surfaces
- A large number of third-party or partner integrations
- Numerous external-facing APIs consumed by customers or partners
- Regulatory or compliance requirements that mandate continuous security validation

How to choose an AI pentesting platform for API environments
Not all AI pentesting tools are designed with APIs in mind. Many are built on top of traditional web application scanners, which can limit their effectiveness in API-first architectures.
When evaluating an AI penetration testing solution for APIs, consider the following:
- API-native testing: Designed specifically for APIs
- Broad protocol support: Works with multiple API protocols and architectures
- Thorough discovery: Can find shadow and zombie APIs
- Multiple API specification formats: Accepts different spec types such as OpenAPI, Swagger, GraphQL schemas, and others
- Authentication workflow support: Allows configuring complex authentication flows
- Session and workflow simulation: Maintains session context and executes multi-step API interactions
- Cross-endpoint vulnerability correlation: Correlates findings across endpoints to discover possible chained attacks
- Finding validation and prioritization: Automatically verifies and prioritizes exploitable vulnerabilities
- Testing integration: Safely executes within staging, production, and CI/CD environments
- Operational efficiency: Scales easily with straightforward deployment and onboarding
Why Equixly is built for AI pentesting of API-first architectures
Equixly is engineered around the reality that APIs are the architectural bedrock of the modern digital landscape. Whether it is a traditional web application, an intelligent generative AI system (GenAI), or a distributed environment making use of the model context protocol (MCP), the underlying communication almost always happens through an API.
By focusing its offensive capabilities here, Equixly provides a universal security layer that protects the very substrate where data flows and business logic resides, ensuring that vulnerabilities are identified regardless of the front-end interface or the complexity of the back-end AI model.
To secure this complex ecosystem, Equixly has developed a suite of capabilities designed for the scale and speed of modern API-first development:
- ‘Agentic AI Hacker’: Functions as an autonomous testing entity powered by a proprietary reinforcement learning algorithm to move beyond basic fuzzing techniques.
- State-aware logic testing: Maps complex business logic and multi-step sequences to identify deep-seated logic flaws like BOLA.
- Shadow and zombie API discovery: Identifies undocumented API versions, obsolete versions (
/v1,/v2, or/beta), and shadow parameters (like hiddenisAdminflags) by comparing active test results against API specifications. - Advanced protocol probing: Detects verb tampering and the use of undocumented HTTP methods that threat actors can use to bypass security controls.
- Multiple inventory ingestion paths: Supports importing HAR and Burp history files, allowing users to discover and inventory APIs directly from recorded traffic.
- CI/CD and DevOps integration: Shifts security left by integrating directly into pipelines and tools like Jira, GitHub, and Slack for near-real-time results that keep pace with software updates.
- Executive and technical reporting: Generates auditable PDF or CSV reports. These contain a business-aligned “Executive Summary” for risk disclosure alongside a “Detailed Security Issues” section with proof-of-concept demonstrations and remediation guidance to help meet SLAs.
Conclusion
AI penetration testing is a natural development of pentesting in a world defined by fast software delivery and API-first architectures. It combines autonomous exploration, attack emulation/simulation, and continuous validation, making it possible for organizations to test their systems at the same pace they build them.
As APIs have become the nervous system of modern applications, to implement AI pentesting effectively, you must leverage purpose-built solutions that have the same starting point as most modern software — application programming interfaces. With API-native capabilities and continuous, state-aware testing, you can progress from periodic security snapshots to ongoing insights into your actual security posture.
Reach out to Equixly to explore AI-powered penetration testing for modern API environments.
FAQs
How does AI penetration testing differ from traditional vulnerability scanning tools?
AI penetration testing actively explores applications, learns behavior patterns, and simulates attack paths, whereas traditional scanners rely mainly on predefined signatures and rule-based testing.
What is the relationship between AI penetration testing and human security experts?
AI pentesting automates large-scale continuous testing, but human experts remain essential for complex architectural reviews, advanced threat modeling, and sophisticated red-team engagements.
Why should APIs be a primary focus in AI penetration testing?
Because APIs handle the majority of application data exchange and business logic, they are a critical part of the modern attack surface.

Zoran Gorgiev
Technical Content Specialist
Zoran is a technical content specialist with SEO mastery and practical cybersecurity and web technologies knowledge. He has rich international experience in content and product marketing, helping both small companies and large corporations implement effective content strategies and attain their marketing objectives. He applies his philosophical background to his writing to create intellectually stimulating content. Zoran is an avid learner who believes in continuous learning and never-ending skill polishing.